IdentityShield Summit '26
Powered by miniOrange — India's premier platform for AI-powered identity security. Our CEO Shivani Tikadia took the arcon stage as a featured speaker, and the SecComply team hosted a booth where we met cybersecurity leaders, policymakers, and defence officials from across the country.
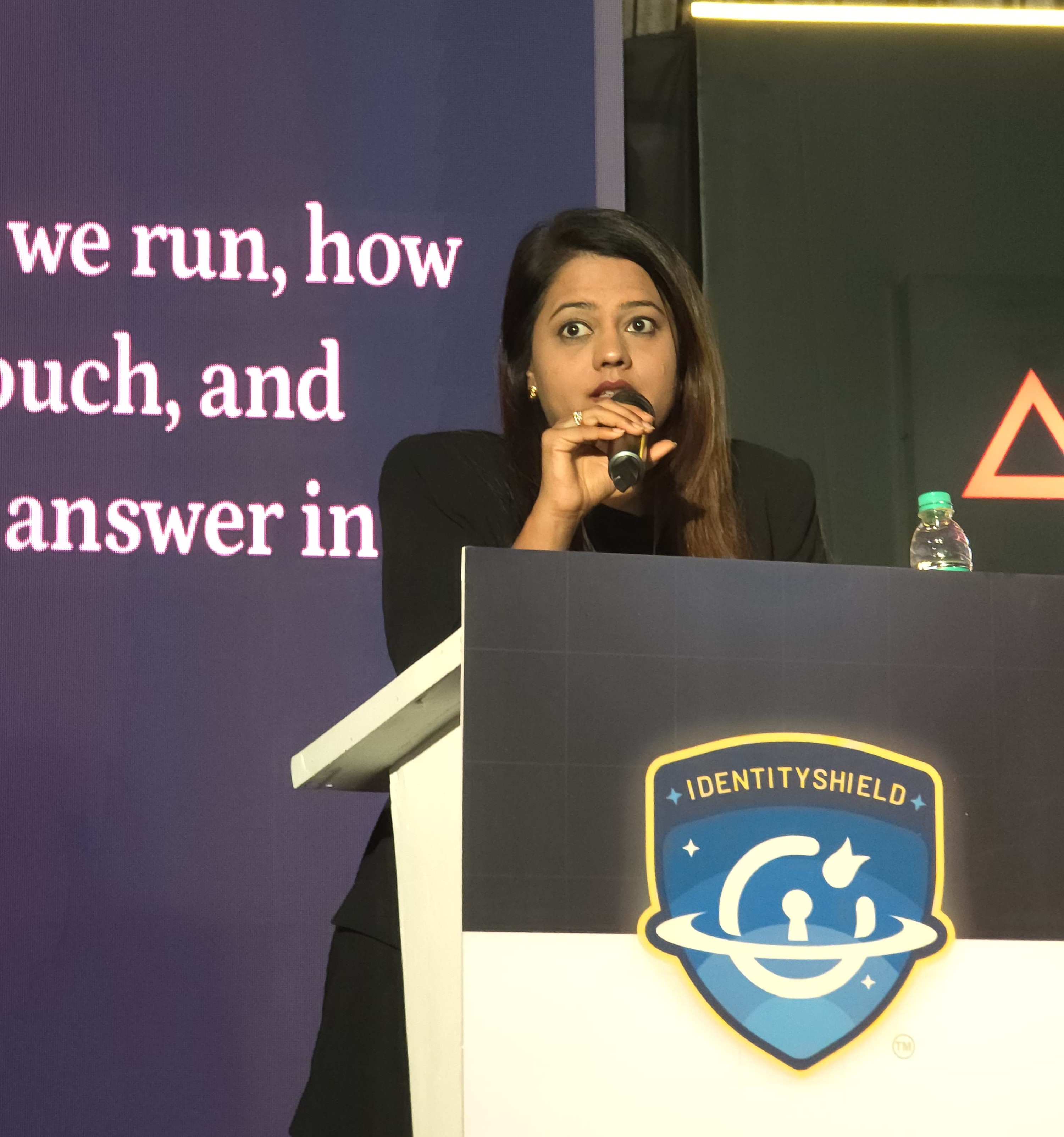
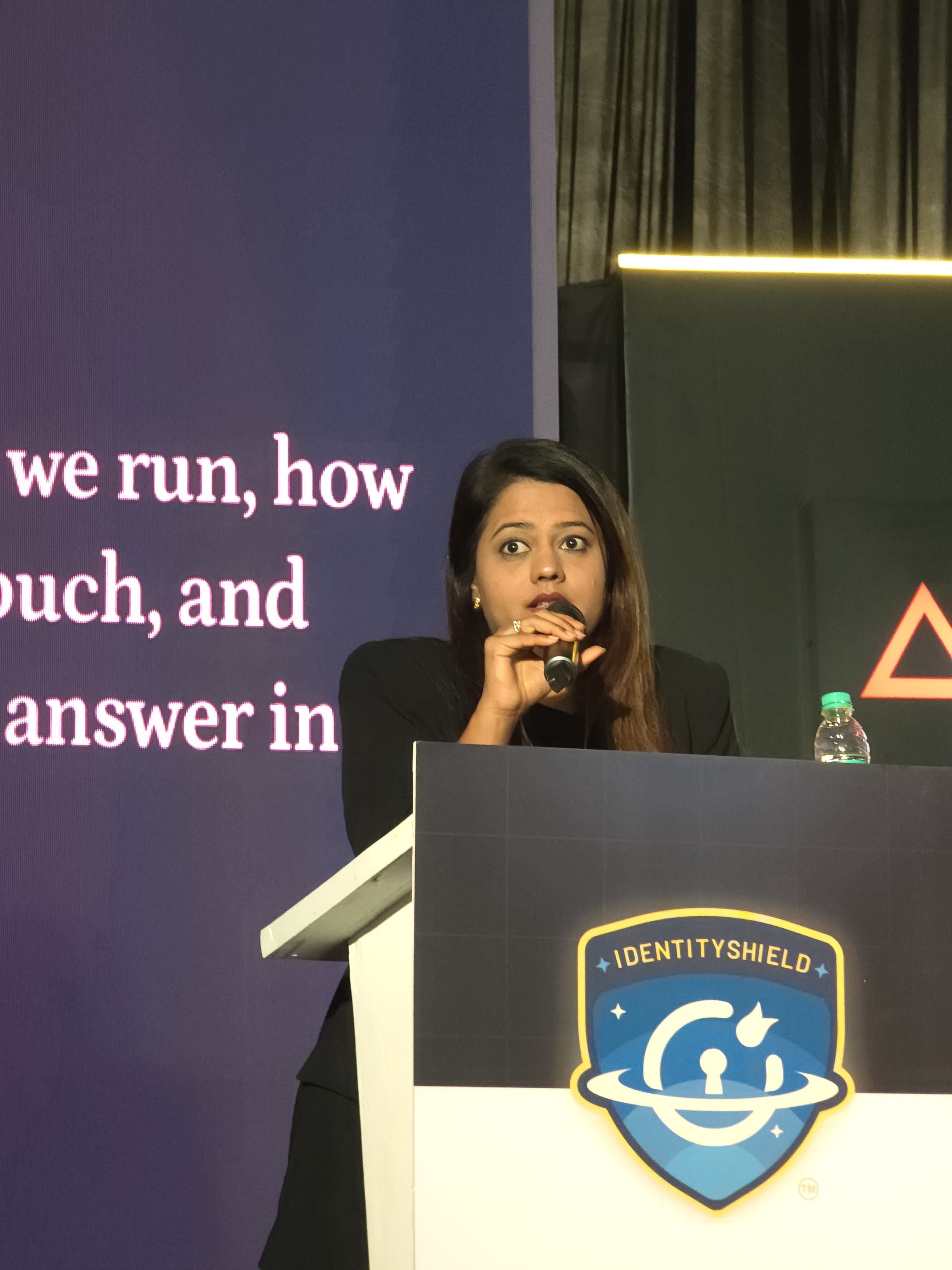
Our Keynote — Shivani Tikadia

Shivani Tikadia
CEO & Founder, SecComplyShivani is a seasoned cybersecurity advisor with 10+ years of experience, trusted by 100+ organisations including 50+ Fortune 500 companies. She is known for helping businesses translate complex security and compliance requirements into practical, scalable, and business-aligned solutions.
At IdentityShield '26, Shivani spoke on the arcon stage about the operational reality of modern compliance programmes — what it takes to run one, how long it takes, and how to answer in a regulator-ready way. Her session drew security leaders, CISOs, and compliance practitioners looking to move beyond policy theatre into real, audit-grade execution.
Beyond consulting, Shivani actively contributes to the cybersecurity ecosystem through her YouTube channel The Nadkarnees, where she regularly shares expert insights, discussions, and podcasts on cybersecurity, governance, risk, compliance, and emerging industry trends — bridging the gap between technical security and business leadership.
Session Highlights
Four anchor points from Shivani's keynote that landed hardest with the audience — and sparked the longest conversations at the booth afterwards.
Why Most Compliance Programmes Fail
Policy documents without operational rehearsal. Controls that live in a binder but not in the engineering pipeline. The most common failure is not lack of effort — it is programmes that look good on paper but cannot survive a real audit.
The Real Timeline to ISO 27001
Most founders hear "six months" and plan accordingly. Reality: 4-9 months for a tight-scope SaaS, 9-15 months for broader enterprise scope. The variance is almost entirely about scope discipline and organisational readiness.
Running ISO 27001 + DPDP + GDPR Together
Overlap is high — but not 100%. The right architecture maps control families across all three frameworks, implements each control once, and generates evidence that satisfies multiple auditors simultaneously.
Answering "What Would a Regulator See?"
The practical litmus test for any compliance programme. If a supervisory authority walked in tomorrow, what documentation exists? What evidence proves controls operated? Most programmes cannot answer cleanly — and that is the real gap to close.
Two Days, Two Themes
Foundations & Strategic Direction
Opening day set the tone with strategic discussions around India's cybersecurity sovereignty and foundational frameworks.
- Keynote from miniOrange founder on reducing foreign cybersecurity dependency
- Zero Trust and IAM architecture sessions for enterprise deployment
- SecComply booth opens — client conversations across ISO, SOC 2, DPDP
- Evening networking with CISOs, policy makers, and defence officials
Implementation & The Operational Reality
Day two moved from frameworks to implementation — where Shivani's session on the arcon stage fit squarely into the programme.
- Shivani Tikadia speaks on compliance programme operational realities
- Panels on AI-driven threats and post-quantum cryptography
- miniTalks — podcast-style interviews with industry leaders
- Closing sessions and the IdentityShield '26 innovation awards
What We Covered On Stage
The IdentityShield Summit '26 convened around the core themes shaping India's cybersecurity future. Here are the topics that framed our conversations on stage and at the booth.
Zero Trust Frameworks
Moving from perimeter-based models to identity-first architectures — and the operational realities of rolling it out.
Identity & Access Management
Modern IAM as the foundation of every serious security programme. MFA, role-based access, and privileged access at scale.
AI-Driven Cyber Threats
How adversaries are weaponising AI — and how defenders are using the same technology for faster detection and response.
Post-Quantum Cryptography
Preparing cryptographic infrastructure for the quantum era before the transition becomes urgent rather than strategic.
DPDP & Compliance Reality
Operationalising the DPDP Act, ISO 27001, and GDPR in the same programme — without duplication and without drift.
Indigenous Cyber Capability
India's path from cybersecurity service provider to global producer — and what the talent ecosystem needs to get there.
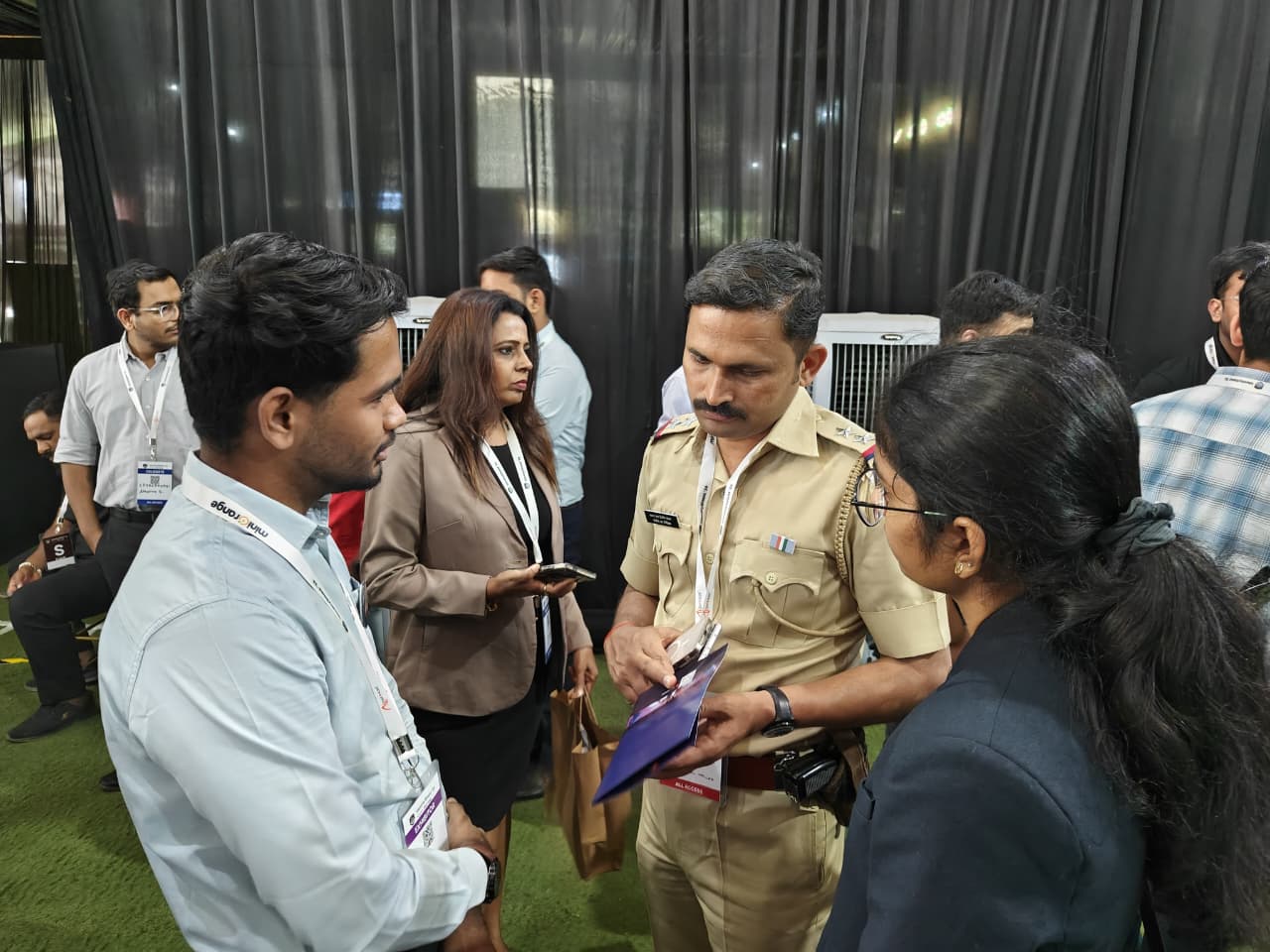
Who We Met at the Booth
Our exhibitor booth drew a cross-section of the Indian cybersecurity ecosystem. Here is who stopped by — and what they wanted to talk about.
Event Gallery
Two days. One stage. Countless conversations. Click any image to view full-size, and move your cursor across the tiles for a little parallax.




















🎯 Key Takeaways From IdentityShield '26
- India is moving fast on indigenous cyber capability.The policy signal from the summit was clear — reducing foreign tool dependency while building home-grown IAM, SIEM, and compliance platforms. Expect more procurement preference for Indian-built solutions in the next 18 months.
- DPDP is now a boardroom conversation.The DPDP Act has moved from "legal team problem" to "CEO agenda item" faster than GDPR did in Europe. Enterprise buyers in India are asking DPDP-specific questions in every vendor evaluation.
- AI-native threats are outrunning traditional controls.Deepfake social engineering, AI-generated phishing, and automated reconnaissance are already bypassing the basic controls most mid-market companies rely on. The defensive AI arms race has started.
- Compliance fatigue is real — but avoidable.Companies running ISO 27001 + SOC 2 + DPDP + GDPR separately are burning out their security teams. Integrated programmes with shared controls, unified evidence, and single-source-of-truth documentation are the only sustainable path.
Why We Show Up
SecComply exists because security and compliance should not feel like translation work. Events like IdentityShield '26 are where we meet the people living that translation problem every day — the CISOs running audits with six frameworks in scope, the founders trying to close enterprise deals faster, the engineering leaders who want privacy built into the product rather than bolted on afterwards. Those conversations shape what we build.